
In our previous chapter of CISSP training online, we learned about incident response, the forensics, types of evidence, Spared and RAID, clustering, and the web farms, backups, additional data redundancy… We are continuing with our CISSP course, and we are at the last chapter. Don’t give up now, become a CISSP, with our CISSP course Syllabus.
In chapter 8 we are going to talk about Software Development Security. Our objectives will be:
-why is software unsecured?;
-Development Methodologies;
-Common Architectures;
-Adversaries;
-OWASP Top 10;
-Change Management;
-Assessing Vulnerabilities;
-Databases;
-Verification and Validation;
-Secure Disposal.
Why is software unsecure?
A software may be insecured for various reasons. Lack of training, lack of funding, no prioritization of security, security as an afterthought… Lack of training the staff to recognize the potential threats, no funding for security-thinking that its value is more than the damage can be etc. It is important to know that no amount of money is much because the damages can be harsh and sometimes even not fixable.
Development Methodologies
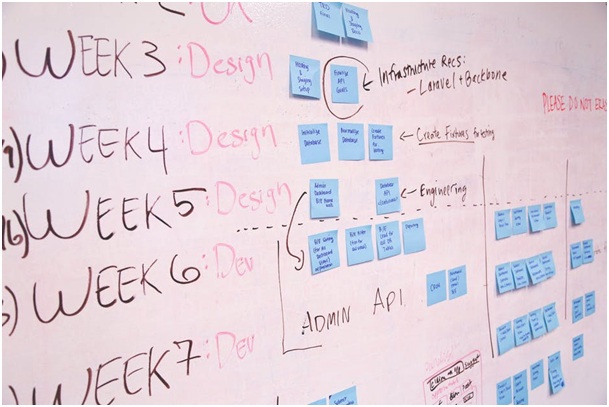
The next level of keeping our system safe is to figure out which type of methodology will work for us. We have Waterfall, Prototype, Spiral, and Agile.
The benefits of the Waterfall are that each phase has specific deliverables and a review process, phases are proceeded and completed at one time. It is best for small projects where requirements are very well understood. Also, it reinforces ”define before design” and ”design before code”.
The cons are that it’s adjusting scope during the life cycle which can kill a project. Also, no working software is produced until late during the life cycle. It has high amounts of risk and uncertainty. It’s a poor model for long and ongoing projects, also if there is a high probability of change.
Prototyping. The good thing is that the software designer and implementer can obtain feedback from the users early in the project. Also, the client and the contractor can compare if the software made matches the software specifications, according to which the software program is built. Besides that, it allows the software engineer some insight into the accuracy of initial project estimates and whether the deadlines and milestones proposed can be successfully met.
Its cons are that clients can rarely understand all the ramifications of proposed changes.
Spiral. It has a high amount of risk analysis and is good for large and mission-critical projects. Cons are those that it can be a costly model to use, and the risk analysis requires highly specific expertise.
Agile. It has great flexibility and immediate feedback. The problem is about the less focus on the system design.
Common Architectures
We’re going forward to take a look at the security and common architectures. There we have distributed computing, service oriented architecture, rich internet application, ubiquitous computing and cloud architecture.
Let’s start with the first one. Distributed computing. It is all about client vs server (thin vs fat clients, scalability, availability, security and so on). Then, we have P2P, which is frequently used for file sharing, channel security, data confidentiality etc.
Service oriented architecture. It’s an architecture and a vision on how heterogeneous applications should be developed and integrated into the enterprise. Sharing a formal contract, loosely coupled, abstraction, composable etc., those are all elements of SOA.
Rich internet applications. When we talk about this one, we have to take a look at the client side threats and server side threats. The client side threats are XSS and CSRF, and the server side threats are code injection, validate input, aggregation and interface, masking and polyinstantiation.
Ubiquitous computing. It’s also known as pervasive computing. Computers are everywhere, whether you look at the wireless technology, or radio frequency ID, near field communication, location based services…
Monitoring and Auditing
When the software is out to the traffic, we want to monitor it. Monitoring validates compliance to regulations and other governance requirements. Also, it demonstrates due diligence and due care on the part of the organization towards its stakeholders. Providing evidence for audit defense, assisting in forensics investigations while collecting and providing the requested evidence and much more.
Besides that, it ensures that the confidentiallity, integrity, and availability of software are safe. It validates the overall state of security.
Monitoring needs to have characteristics of good metrics, which include consistency, quantitative, objectivity, relevance, and inexpensiveness.
Now, we’re coming to auditing. Audits are very important detective controls and can be used to correlate information after the event. They can be used to ensure policies are being followed and that they’re effective. Making sure that individual user accounts
aren’t unintentionally being allowed to accumulate rights of permissions. It also checks the accuracy and completeness of transactions that are authorized.
Adversaries and Review
Who are adversaries? You have probably heard about Script Kiddies, hackers, elite… There are many more of them, such as non-structured, structured or highly structured adversaries.
The structure of the attack can be used to address skill set of the attacker, but also the format and organization of data being addressed. When you figure out who is targeting your data, in that case only you will know how much protection is necessary.
OWASP 1 through 5
We already learned about why is software unsecure. Vulnerability data bases and resources are OWASP, CWE, CVE, NVD, and US CERT.
OWASP stands for The Open Web Application Security Project. It’s an international organization dedicated to enhancing the security of web applications. They have numerous security related projects. One of the most popular is being the top 10 project.
1.Injection. Injection techniques might be used by a hacker to gain access to otherwise protected data. You can use IBM Security AppScan to find and eliminate this vulnerability.
2.Broken authentication and session management. One of the most commonly exploited web vulnerabilities. You can use AppScan to identify these potential problems.
3.Cross-site scripting. Hackers use XXS to send malicious codes to websites. IBM Security AppScan can also search and detect those malicious codes.
4.Insecure direct object reference. If the users don’t properly vet their values, hackers can use them to pass malicious commands to the site.
5.Security misconfiguration. Misconfigured web servers provide hackers with opportunities to abuse many websites.
OWASP 6 through 10
6.Sensitive data exposures. The unencrypted data in transport can be vulnerable to attackers listening in on a connection.
7.Missing function level access control. It occurs when a lower level access user is inadvertently allowed access to a part of the website restricted to higher level access.
8.Cross-site request forgery. Commonly exploited vulnerability. It’s a web application vulnerability that makes it possible for the attacker to force a user to unknowingly perform actions while they’re logged into an app.
9.Heartbleed and Shellshock in action. These are the most recent examples of the 9th vulnerability, for your better understanding we used them as samples. Reusable software components available to app developers. Many of those are open source, and available for free.
10.Unvalidated redirects and forwards. Commonly exploited vulnerability type. Web apps redirect and forward users to other pages with suspicious content. All of the types we mentioned can be prevented with IBM Security AppScan.
Defensive Coding
Let’s start with the definition. The defensive coding is a form of proactive and secure coding intended to ensure the continuing function the software under unforeseen circumstances. The benefits of coding generally improve general quality, make the source code comprehensible and make the software behave in a predictable manner.

Input validation of defensive coding corrects data type and format, falls within the expected and allowed range of values and is not interpreted as a code when it shouldn’t be.
Sanitization converts something that is considered dangerous into its safe form. It has two types-stripping and substitution.
Change Management
We already talked a lot about the change management in the previous modules, but now we will just repeat that it provides us the stability of the environment. Change management is procedural, scheduling, documentation, awareness, and training, back out plans, CMDB, vendor contacts and support info.
Then we have patch management. Patches are additional pieces of code developed to address problems. They enable additional functionality or address security flaws within a program.
Vulnerability Scans and Penetration Testing
When we take a look at the security testing, we can see that we have white box testing and black box testing. White box is structural analyzing and has full access to source code, design documents, use and misuse cases and configuration files.
Black box testing has no knowledge of the code. It’s also known as the zero knowledge assessment because the testers have no access to supporting documentation or the internal working of the code. There we have fuzzing, scanning, and penetration testing.
Fuzzing is also known as the fault injection testing. Scanning is used to map the environment, to identify server versions, running services or open ports, identify the patch levels and much more.
There is a vulnerability scanning, content scanning, and privacy scanning.
Pen-Tests. We talked a lot about them earlier. Here, the scanning is passive, it looks to actively exploit a weakness.
Verification Validation Certification and Accreditation
Verification-Does the software meet the developer’s description? Also, does it satisfies the requirements?
Validation-Does the software solve the problem that it was supposed to solve and does it meet a real-world need?
When we want to have verification and validation checks, we use all of the stuff we talked about-availability, authentication, authorization and so on.
Certification. It’s the technical evaluation of the security features of a software product.
Accreditation. Management’s acceptance of the product and the decision to implement the software into their environment.
DB Intro and Models
Database management considers database models, relational database components, database integrity and security issues, warehousing, and data mining.
Database models are hierarchical, distributed, object-oriented and relational.
Relational Databases
A form of tables related to each other. It stores data in such a way that data manipulation language can be used independently on data. It uses Oracle, Sybase etc. Its definitions are primary and foreign keys, data dictionary, metadata, view, cell, record, file, schema, turple and attribute.
That’s all for you now, you just have to take your exam. It’s called the Software Development Security Skill Certification Test. Skill level is intemediate, it has 40 questions and you have one hour to complete it. Good luck!
