A wireless medium is vulnerable to various threats. Here we will discuss different kinds of threats and techniques to overcome them. There are the following Wireless Network Threats –
- WAR driving – WAR driving is when someone drives around looking for an unsecured Wi-Fi network with the intention of breaking in to access confidential and important information. This can be prevented via strong wireless security such as using strong wireless encryption on networks.
- WEP/WPA cracking – Another threat is WEP/WPA cracking. This is when weaknesses in the encryption key could allow cracking into Wi-Fi.
- Rogue Access Points – Rogue access points are set up for users to connect so traffic can be captured and sniffed. However, they can be very problematic as they allow for rogue devices to connect to a network which can create issues for devices that are already connected to the network. It needs to be made clear that people are not allowed to bring their own personal devices and set up their own access points on a network. Issues can be mitigated by not connecting to devices you don’t recognize or open wireless access points.
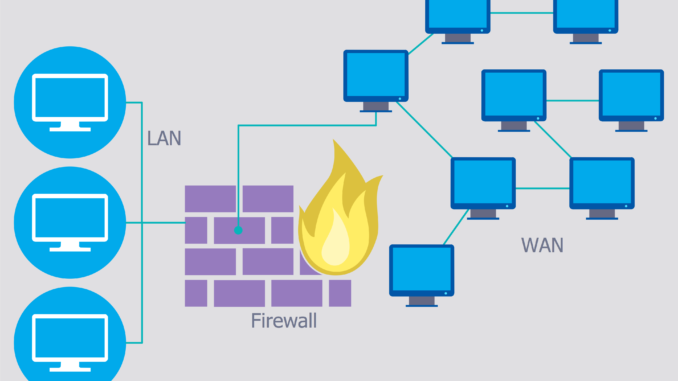
Non Wireless Attacks – Non wireless attacks are actual attacks against a network.
- Denial of Service (DoS) – One such attack is a Denial of Service (DoS) which is an attack on services and resources and blocks host generating traffic. There is also a Distributed Denial of Service (DDoS). These are harder to fix as multiple hosts are performing DoS.
- Man in the Middle Attack – In this kind of attack, the attacker listens, captures and impersonates a user which allows them to pass on false certificates and capture data that is out on an HTTPS web page.
Social Engineering and other attacks – Social engineering exploits weakness in people which allows attackers to find vulnerabilities. There has to be mandatory user training so employees know policies on things such as leaving a computer unlocked, giving out passwords or opening doors for unknown people. Other forms of attacks are viruses, worms, and buffer overflow. Companies install anti-malware on computers to mitigate viruses as well as implementing user policies such as do not use unknown devices such as a USB just found on the floor. Worms are dangerous to networks because they can replicate quickly and take down a network by performing a constant denial of service. A buffer overflow is a vulnerability in a program that can write more program than can fit into a program so instead of fault finding, there is an overwriting after a buffer than can cause a crash.
Traffic Sniffing, FTP Bounce and Smurf – Packing sniffing involves capturing network traffic. A way to mitigate packet sniffing is to secure WiFi, eliminate hubs and encrypt traffic. File transfer protocol bounce connects to FTP server with port to specify port on another client. FTP bounce sends data to open port on specific client. Smurf sends a forged ICMP packet into the network specifying broadcast recipient. Smurf attacks have mostly been eliminated by advancements in routers and how we respond to ICMP echo requests.