Here are the steps to perform denial of service –
Download slowloris – Open a browser and Google ‘slowloris’. Click on the Github link. Click on slowloris. The code will open up. Make it a raw file and copy the code. Close the browser and open a text file and copy the code. Save the file as slowloris.pl as it is a Perl script, on desktop.
Prepare the victim – Make a test site on the victim i.e. Windows 10 virtual machine here. Run it on a browser and see that it is running perfectly. This test site here is running on Ubuntu server.
Create a syn flood – Now to implement denial of service attack, we will create a syn flood using slowloris.pl. Open up a terminal on the Kali Linux machine. Change the directory to desktop. Run the ls command, and it shows slowloris.pl. Enter the command to run the Perl script –
perl slowloris.pl -dns 192.168.1.16
The IP address is of the server that we are attacking. Run the script.
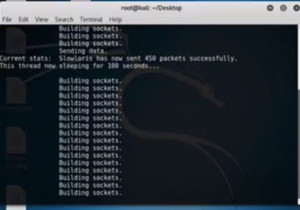
Figure 1. Perl script output
Here we can clearly see that it is opening a whole bunch of some connections to the actual website so that no other resources can actually make connections.
On the Windows 10 machine if we give ss4 socket state command at the server, we can clearly see that there are multiple connections being made from 103 which is the machine on 106 and all on HTTP. When the admin tries to open the website it will not open. That means we have effectively done denial of service on this website using ‘slowloris’ tool.
Preventing Denial of Service Attacks – If we have a web application firewall or a firewall protecting this web server, we can filter any traffic coming from 103 and also set a rule saying not to allow too many concurrent connections from a single IP address. This would prevent denial of service. However, if we had ten thousand machines running slowloris, this would be very difficult to actually prevent and there security people are needed.
Ethical Hacking Tutorial: Denial of Service Lab Session Video:
